Want to know Passleader PCCSA Exam practice test features? Want to lear more about Paloalto-Networks Palo Alto Networks Certified Cybersecurity Associate certification experience? Study Certified Paloalto-Networks PCCSA answers to Avant-garde PCCSA questions at Passleader. Gat a success with an absolute guarantee to pass Paloalto-Networks PCCSA (Palo Alto Networks Certified Cybersecurity Associate) test on your first attempt.
Paloalto-Networks PCCSA Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
What does Palo Alto Networks Traps do first when an endpoint is asked to run an executable?
- A. send the executable to WildFire
- B. run a static analysis
- C. run a dynamic analysis
- D. check its execution policy
Answer: D
NEW QUESTION 2
Company policy allows employees to access the internet. While searching for office supplies on the internet, a corporate user mistypes a URL, connects to a malicious website, and unknowingly downloads malware.
Which action should have been taken to prevent the malware download but still allow user access to the internet?
- A. deploy a firewall with content filtering capabilities on the corporate perimeter
- B. allow only encrypted HTTPS access to the internet
- C. configure digital certificates for all users to authenticate internet downloads
- D. permit web connections only to TCP port 443
Answer: A
NEW QUESTION 3
What method can be used to guarantee that a document originates from you and no one else?
- A. public key encryption, encrypting the document with the private key and making the public key available to others
- B. symmetric encryption, ecnrypting the document with the secret key and making a different secret key available to others
- C. symmetric encryption, ecnrypting the document with the secret key and making the same secret kay available to others
- D. public key encryption, encrypting the document with the private key and making the private key available to others
Answer: A
NEW QUESTION 4
Match the common TCP/IP protocol with its corresponding port(s).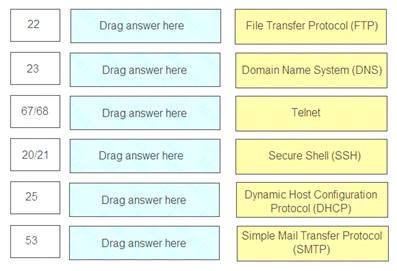
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
22 – Secure Shell (SSH) 23 – Telnet
67/68 – Dynamic Host Configuration Protocol (DHCP) 25 – Simple Mail Transfer Protocol (SMTP)
53 – Domain Name System (DNS)
NEW QUESTION 5
Which type of firewall monitors traffic streams from beginning to end?
- A. circuit-level gateway
- B. stateless
- C. stateful
- D. packet filter
Answer: C
NEW QUESTION 6
Which type of cloud computing deployment makes resources exclusively available to members of a single organization?
- A. local
- B. private
- C. hybrid
- D. public
Answer: B
NEW QUESTION 7
To which type of organization does the PCI DSS apply?
- A. any organization that accepts, transmits, or stores any cardholder data
- B. organizations that only accept cardholder data regardless of size or number of transactions
- C. only organization larger than 100 employees that accept, transmit, or store any cardholder data
- D. organization that only transmit data regardless of size or number of transactions
Answer: A
NEW QUESTION 8
Which two types of SaaS applications are allowed by an IT department? (Choose two.)
- A. tolerated
- B. certified
- C. sanctioned
- D. unsanctioned
Answer: AC
NEW QUESTION 9
Which type of security device uses a single-pass, parallel processor hardware architecture to accelerate content inspection?
- A. unified threat management
- B. stateless firewalls
- C. next-generation firewall
- D. PoS-based firewall
Answer: C
NEW QUESTION 10
What does a hypervisor enable?
- A. high-speed searching of already aggregated security log files
- B. high-speed aggregation and viewing of security log files
- C. multiple physical machines to be configured into a high-performance cluster
- D. multiple guest operating systems to run on a single physical machine
Answer: D
NEW QUESTION 11
What is a component of a public key infrastructure?
- A. Key Distribution Center
- B. KDC ticket
- C. SSH key
- D. certificate authority
Answer: D
NEW QUESTION 12
In which type of cloud computing service does an organization own and control application data, but not the application?
- A. platform as a service
- B. computing as a service
- C. infrastructure as a service
- D. software as a service
Answer: D
NEW QUESTION 13
Match each option with the term it describes.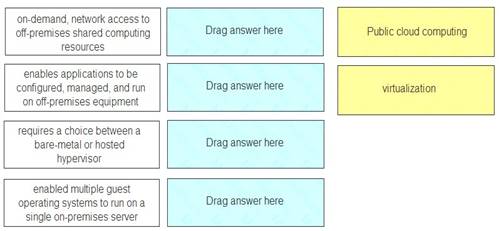
- A. Mastered
- B. Not Mastered
Answer: A
Explanation:
Public-cloud computing Public-cloud computing Virtualization Virtualization
NEW QUESTION 14
What is the function of a hashing protocol?
- A. encrypts data with encapsulation
- B. establishes an unencrypted tunnel
- C. establishes a secure tunnel
- D. provides data integrity
Answer: D
NEW QUESTION 15
Which well-known port is associated with the Simple Mail Transfer Protocol?
- A. 143
- B. 25
- C. 997
- D. 40
Answer: B
NEW QUESTION 16
Which type of attack floods a target with TCP SYN requests?
- A. route table poisoning
- B. reconaissance
- C. denial-of-service
- D. IP spoofing
Answer: C
NEW QUESTION 17
What is the primary purpose of using encryption as part of your network data security architecture?
- A. authorization
- B. confidentiality
- C. integrity
- D. authentication
Answer: B
NEW QUESTION 18
......
100% Valid and Newest Version PCCSA Questions & Answers shared by Allfreedumps.com, Get Full Dumps HERE: https://www.allfreedumps.com/PCCSA-dumps.html (New 50 Q&As)